Top 10 SIEM Vendors Shaping Modern Security in 2026
A practitioner's guide to the SIEM landscape, with an argument for why the data layer underneath your SIEM matters more than anything on the feature comparison page.

Security data has gotten bigger, faster, and more expensive every year since SIEMs were invented. The teams trying to defend modern cloud environments are working with tools designed for a world that doesn't exist anymore. That gap is what "modern SIEM" actually means, and it's the reason the vendor landscape has shifted so much in the past few years.
What a SIEM actually does (in 2026)
A SIEM (Security Information and Event Management platform) collects logs from across an environment, stores them, makes them searchable, and runs detections against them to flag suspicious activity. That definition has been stable for 20 years. What has changed is everything around it.
Environments are almost entirely cloud-based now. A typical mid-market security team is pulling logs from AWS, GCP, Azure, Okta, GitHub, Slack, EDR tools, SaaS apps, and a long tail of internal services. Volumes measured in hundreds of gigabytes per day used to be an enterprise problem. Now it's where a Series A startup starts.
The modern SIEM has to ingest at cloud scale, store data affordably for compliance timeframes (12+ months for most frameworks), search it fast during an incident, and run detections that don't drown analysts in false positives. It also has to play well with AI, pipelines, and whatever comes next.
Modern data + modern security: Why it matters
The SIEM market is quietly splitting into two camps.
On one side are platforms built on modern data infrastructure: columnar storage, cloud-native architecture, storage-based pricing, SQL-compatible query languages, and AI workflows designed from day one. On the other side are platforms carrying 10-20 years of architectural decisions forward, retrofitted for the cloud but still shaped by the constraints of on-prem appliances and per-GB ingest pricing.
You can ignore this split during a demo. You can't ignore it once you're running at scale. Data architecture determines how fast your queries run, what you can afford to collect, how painful it is to add a new log source, and whether AI actually helps your team or just produces confident-sounding nonsense.
When the data layer is right, everything downstream gets better. Detections are easier to write and tune. Investigations with LLMs take minutes instead of hours. Security teams can keep more logs for longer without setting off a budget alarm. AI works because the data is clean, normalized, and queryable at speed.
That's what "modern data + modern security" means: it's the lens worth using as you evaluate any vendor on this list.
1. RunReveal
RunReveal is the unified AI-native security data platform built for modern security teams. It handles log ingestion, pipelines, detection, case management, dashboards, and AI-powered investigation in one stack, so teams can stop stitching together a SIEM, a pipeline tool, a data lake, and a SOAR platform to get the workflow they actually want.
The product is built on ClickHouse, a columnar database used by some of the most data-intensive companies in the world (including RunReveal customers like ClickHouse itself, Cursor, Harvey, Temporal, Sentry, and Lumos). That foundation is why RunReveal can offer storage-based pricing: you pay for what you keep, not for every byte that passes through ingest. Teams that switched from legacy SIEMs typically save tens of thousands of dollars a year by filtering low-value data with native pipelines, before it ever hits storage.
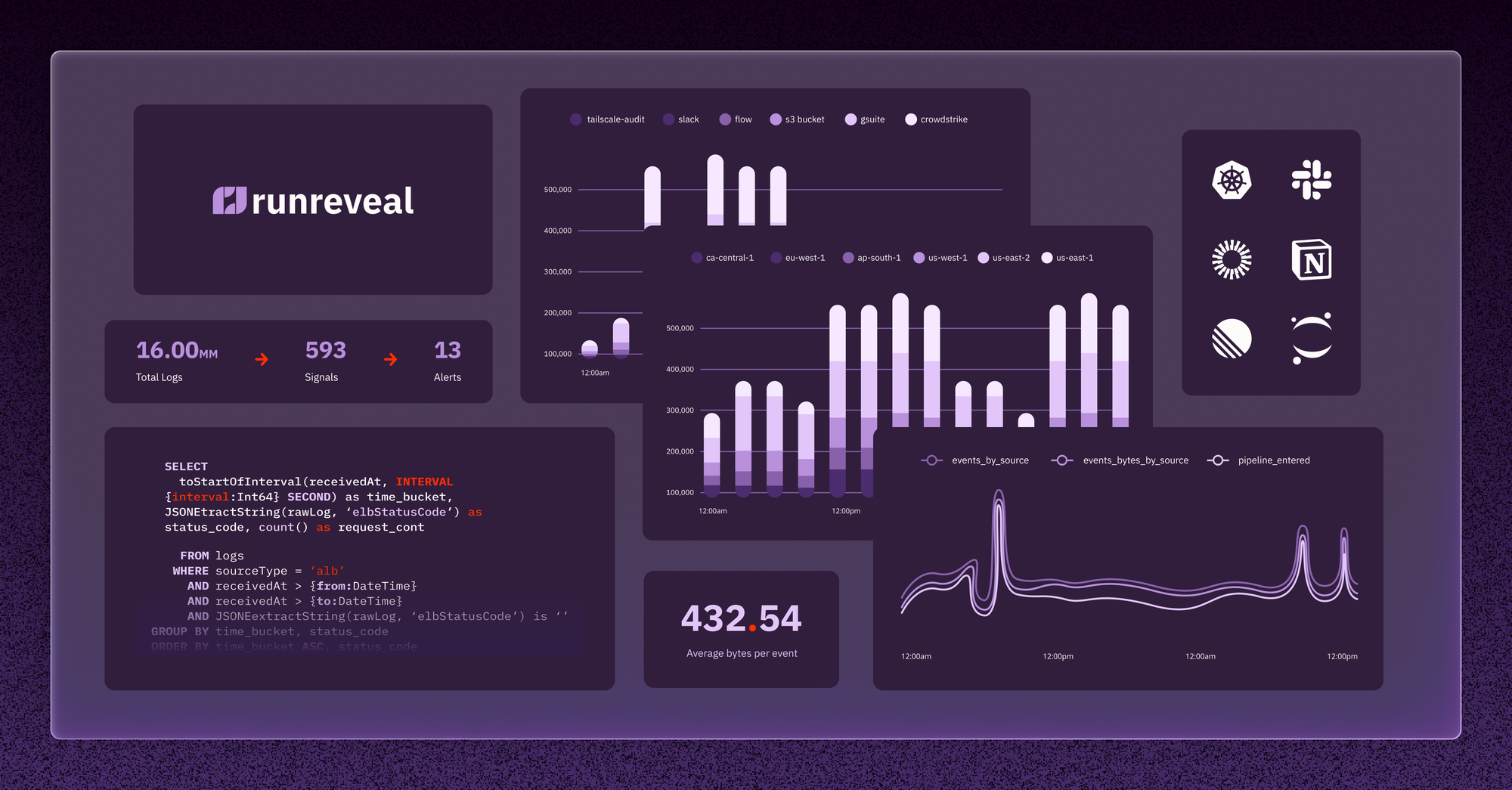
Platform at a glance:
- Storage-based pricing: You pay for what you store, not what you ingest. Noise is cheap to drop.
- Built on ClickHouse: Columnar architecture designed for high-volume analytical queries.
- SQL-compatible query language: Familiar syntax for analysts, engineers, and developers.
- Native Pipelines: Enrich, filter, transform, and route data before it lands in storage.
- AI-native from day one: The Autonomous Security Operation Agent investigates alerts, runs queries, and documents its reasoning in cases with full transparency.
- Flexible deployment: Cloud-native SaaS, Bring Your Own Cloud, Bring Your Own Database, on-prem, or dedicated cloud.
Core problems RunReveal solves:
- Cost vs. coverage tension: Storage-based pricing and native pipelines let teams collect everything they need without a punitive bill.
- Tool sprawl: One stack replaces the usual SIEM + pipeline tool + data lake + SOAR patchwork.
- Slow investigations: SQL-compatible search on ClickHouse returns results in seconds, and the AI agent can carry investigations end-to-end.
- Long onboarding: Most teams are live in days, not weeks, without a mandatory professional services engagement.
Testimonials:
"I can add a new source, write the detection, read queries, find the data that I want, and wire it up to get alerts for it, all within an hour or two. Pretty great compared to existing tool stacks that would be weeks or more." Travis McPeak, Security, Cursor
"RunReveal is our cloud security partner in crime. Their expertise in data security and commitment to technical collaboration is why ClickHouse selected RunReveal over legacy SIEM solutions." Julio Jimenez, Cloud Security Lead, ClickHouse
2. Splunk (Cisco)
Splunk is the SIEM most people in security have used at some point. It's a powerful data analytics platform with strong dashboards, a mature app ecosystem, and a proven track record in large enterprises. Since Cisco's 2024 acquisition, Splunk has continued to tighten its integration with Cisco's broader security portfolio.
Features:
- Splunk Enterprise Security: Mature correlation, dashboards, and reporting built on SPL.
- Adaptive Response: Orchestrates response actions across connected tools.
- Machine Learning Toolkit: Lets teams build custom ML models for anomaly detection.
- Deployment flexibility: On-prem, Splunk Cloud, or hybrid.
- App marketplace: A large ecosystem of integrations and pre-built content.
The trade-off most teams discuss: Splunk's per-GB ingest pricing scales linearly with data, which makes it hard to collect everything you might want to. Many Splunk shops also adopt Cribl or a similar pipeline tool to route, filter, and shape data before it hits Splunk, which helps with cost but adds another contract to manage.
3. Microsoft Sentinel
Microsoft Sentinel is the native SIEM for Azure environments, with strong integration into the broader Microsoft security stack (Defender, Entra ID, Purview). It's a sensible default if most of your identity and infrastructure already lives in Microsoft.
Features:
- Deep Microsoft integration: Pulls logs and signals from Defender, Entra ID, Office 365, and Azure with minimal setup.
- KQL (Kusto Query Language): Powerful for complex analytical queries once you learn it.
- Automation via Logic Apps: Orchestrates response through Azure's workflow framework.
- ML-based analytics: Behavioral detection with threat intelligence enrichment.
- Unified data lake and graph: Newer capabilities for cross-source reasoning across connected tenants.
The trade-off: pricing gets complicated fast once you ingest non-Microsoft data at scale, and KQL is yet another query language for teams that don't already live in Azure.
4. Google Security Operations
Google Security Operations (formerly Chronicle) is Google's SIEM, built on the same infrastructure as Google Search. It's designed for large-scale log ingestion with fast search performance, and ships with tight integrations into Google Cloud, VirusTotal, and Mandiant threat intelligence.
Features:
- Hyperscale search: Query years of log data with strong performance.
- VirusTotal and Mandiant integration: Threat intelligence baked into the investigation workflow.
- Unified Data Model: Normalized schema across diverse log sources.
- YARA-L detection language: Purpose-built for writing behavioral detections.
- SOAR via Siemplify: Case management and playbooks included.
The trade-off: pricing is typically volume-based and favors high-ingest enterprises. YARA-L is powerful but becomes yet another query language for teams already juggling SPL, KQL, and SQL.
5. CrowdStrike Falcon Next-Gen SIEM
CrowdStrike Falcon Next-Gen SIEM extends the Falcon platform beyond endpoint into log management and correlation across the broader stack. It's a natural upgrade path for teams already deeply invested in Falcon for EDR.
Features:
- Falcon platform integration: Tight correlation between endpoint telemetry and other log sources.
- Charlotte AI: Conversational AI assistant for triage and investigation.
- Fast search: Built on CrowdStrike's data platform.
- Pre-built content: Detection library aligned with CrowdStrike threat intelligence.
- Native SOAR: Fusion playbooks for response automation.
The trade-off: teams that aren't already on Falcon face a heavier lift to adopt, and costs can grow quickly as you ingest more non-CrowdStrike data.
6. Panther
Panther is a cloud-native SIEM focused on detection-as-code. Detections are written in Python and version-controlled in Git, which appeals to detection engineers who want to treat their rules like software.
Features:
- Detection-as-code: Python-based detections managed in Git.
- Data lake architecture: Built on Snowflake for storage and search.
- Scheduled queries: Run detections on a cadence against stored data.
- Integrations: Strong coverage across cloud and SaaS sources.
The trade-off: Panther often asks you to bring your own Snowflake data lake, which adds another bill and another system to operate. Teams that want a fully managed experience sometimes find the architecture more modular than they'd like.
7. Elastic Security
Elastic Security is built on top of the Elastic Stack (Elasticsearch, Kibana), which many engineering teams already run for observability. That familiarity makes it a popular choice for teams consolidating security and observability data on shared infrastructure.
Features:
- Open source foundation: Self-host or use Elastic Cloud.
- Kibana dashboards: Rich visualization and ad hoc analytics.
- Pre-built detection rules: Mapped to MITRE ATT&CK.
- Machine learning anomaly detection: Supports UEBA-style use cases.
- Integration ecosystem: Beats, Fleet, and a broad integration library.
The trade-off: Elastic is flexible but operationally heavy at scale. Index management, cluster tuning, and cost modeling become real work as your data grows. Teams without strong infrastructure skills often end up paying someone (or several someones) to keep it healthy.
8. Sumo Logic
Sumo Logic is a cloud-native log management and SIEM platform that predates the modern cloud SIEM category. It's a solid option for teams that want a mature SaaS platform covering both observability and security.
Features:
- Cloud SIEM add-on: Detection engine layered on top of log management.
- LogReduce and LogCompare: Pattern detection for noisy logs.
- Continuous intelligence: Real-time analytics across log streams.
- Compliance reporting: Pre-built templates for SOC 2, PCI, and HIPAA.
- Third-party integrations: Broad coverage across cloud and SaaS.
The trade-off: like many volume-based platforms, cost scales with ingest, which gets uncomfortable as cloud log volumes grow.
9. Rapid7 InsightIDR
Rapid7 InsightIDR is a cloud-native SIEM that bundles log management with EDR, UBA, and deception technology in a single platform. Detection and response is the core story, with Rapid7's Insight Agent providing endpoint telemetry out of the box.
Features:
- Attacker Behavior Analytics: Detection content developed from Rapid7's threat intelligence and incident response work.
- Insight Agent: Universal endpoint agent for real-time scanning and EDR-style telemetry.
- Deception technology: Honey users, honey tokens, and honeypots built into the platform.
- Visual investigation timeline: Timeline-based view of attacker activity across sources.
- Custom detection rules: Expanded custom rule authoring and management added in the 2026 release cycle.
The trade-off: InsightIDR's value compounds when you also run Rapid7's endpoint and vulnerability management tools, but the per-asset pricing model can get expensive once your attack surface grows past the platform's sweet spot.
10. Exabeam
After its 2024 merger with LogRhythm, Exabeam is now one of the larger pure-play SIEM vendors, focused on UEBA (User and Entity Behavior Analytics) and combining Exabeam's New-Scale cloud SIEM with the legacy LogRhythm customer base.
Features:
- UEBA at the core: Behavioral analytics for insider threats and account compromise.
- Timeline-based investigation: Visual session reconstruction for analysts.
- New-Scale SIEM: Cloud-native platform that serves as the go-forward product.
- Pre-built content: Detection and correlation rules out of the box.
- SOAR capabilities: Response automation included.
The trade-off: post-merger product consolidation is still ongoing. Customers on legacy LogRhythm offerings have a migration path ahead of them, and teams evaluating Exabeam should confirm which product line they're actually buying into.
Criteria to consider when choosing a SIEM vendor
A few criteria matter more than the feature comparison table. These are the ones worth asking about during any vendor conversation:
- Pricing model. Ask how the vendor prices and what happens to your bill when your cloud environment doubles in size. Ingest-based pricing punishes you for collecting more data. Storage-based pricing gives you room to be thorough.
- Data architecture: The underlying data platform shapes query speed, cost at scale, and how painful it is to run analytical workloads. Columnar storage with cloud object storage underneath has become the modern default for good reason.
- Detection engineering experience: How hard is it to write, test, and tune a detection? What query language does your team need to learn? Can you version-control your rules? These questions decide whether your detection coverage grows over time.
- Pipeline capability: The ability to enrich, filter, and route data before it hits storage has gone from nice-to-have to table stakes. If the SIEM doesn't do it natively, you'll end up buying a separate tool for it.
- AI maturity: AI-native platforms built AI into their workflows from the start. Bolt-on AI often demos well but creates brittle investigation paths during real incidents. Look for transparency (can you see what the AI did and why?) and depth (can it run real investigations, not just summarize alerts?).
- Time to value: How long does a new customer take to go from signed contract to production detections? Days is possible now. Weeks or months means you're paying for the tool before you get value from it.
- Total cost of ownership: Factor in licensing, infrastructure, professional services, third-party tools, and the internal engineering time required to keep the system healthy. The sticker price rarely tells the full story.
- Deployment flexibility and data residency. Some teams can run fully in SaaS. Others need logs to stay inside their own cloud account for compliance, regulatory, or data residency reasons. A few need on-premises deployments for air-gapped or sovereign environments. Ask whether the vendor supports multiple deployment modes with a consistent feature set across all of them. RunReveal runs on Kubernetes and offers cloud-native SaaS, in-VPC (Bring Your Own Cloud), and on-premises deployments, so teams can match the deployment to their security posture without losing product capability.
Conclusion
SIEMs have always been the backbone of security operations. What that backbone looks like in 2026 is different from what it looked like even three years ago. The vendors doing the most interesting work today share a common trait: they're building on modern data infrastructure and designing for how security teams actually work today.
If you're evaluating your options, start with the data layer. Everything else (cost, speed, detection quality, AI capability) flows from that choice. Pick the platform whose architecture matches the shape of your environment, and the rest of your security program will have a lot more room to grow.
If you want to see what a modern data + modern security stack looks like in practice, book a demo with RunReveal or start a free trial.

